Ever seen a computer trip over its own shoelaces? That’s pretty much what happens when a program writes data where it shouldn’t—commonly known as an “out-of-bounds write.” It’s like your code decides to crash a neighbor’s backyard barbecue uninvited and then wonders why everything’s on fire. In the world of software vulnerabilities, CWE-787: Out-of-Bounds Write is a particularly mischievous gremlin that can lead to crashes, data corruption, or even security exploits. This article takes you on a funny but informative journey through the chaos of wayward memory writes and how to keep your code out of the danger zone.
When Memory Rebels: The Slapstick of Rogue Writes
Picture your program’s memory as a tidy row of hotel rooms. Each variable gets a key, a nice clean bed, and the promise of personal space. But then one night, an overenthusiastic line of C code bursts through Room 203’s wall and starts redecorating Room 204 without permission. Congratulations—you’ve just witnessed an out-of-bounds write! It’s the programming equivalent of a sitcom character who mistakes someone else’s apartment for their own and starts cooking spaghetti on the wrong stove. Except, instead of laughter, you get segmentation faults—and maybe a security advisory.
Out-of-bounds writes occur when code scribbles data outside the allocated limits of a buffer. It’s like mailing a letter to an address that doesn’t exist but still expecting someone to open the door. In languages like C and C++, where the training wheels are off and you’re riding downhill at full speed, it’s surprisingly easy to go rogue. A single miscalculated index or unchecked length can turn a harmless array operation into a demolition derby. And the nasty twist? These bugs often hide quietly for months, only showing themselves at the worst possible moment—usually right before a major release.
At their most destructive, these writes don’t just crash a program; they open windows for attackers. Overwriting control structures, function pointers, or return addresses can give an enterprising hacker the chance to execute malicious code. It’s a bit like a mischievous toddler taking over the TV remote—suddenly, chaos reigns. So while “out-of-bounds” might sound like a sports term, in security it’s a recipe for mayhem. And the worst part? The code that caused it often looks perfectly innocent—until it isn’t.
How to Tame the Out-of-Bounds Beast Before It Bites
The first rule of taming a memory gremlin is awareness. Know where your buffers are and how big they are. Before you go writing data, double-check that your indexes and sizes play nicely within the boundaries. Defensive programming is your seatbelt here. If your code deals with arrays or strings, don’t trust any input that comes from the outside world. If someone hands you a “safe” value, verify it like it’s a suspiciously cheap antique. Just one unexpected length value can send your data careening out of its designated box and into forbidden territory.
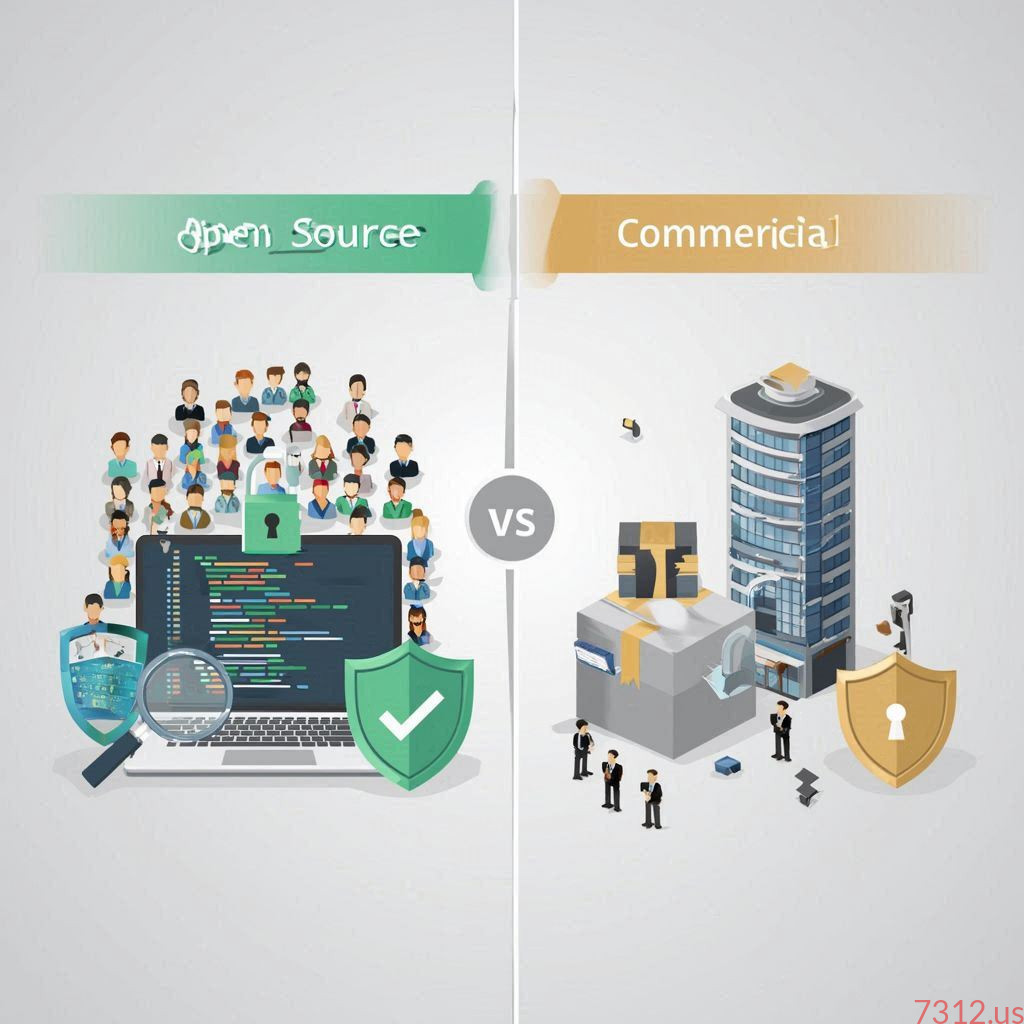
Next, bring in the modern tools and compilers that act as watchdogs for memory mischief. Tools like AddressSanitizer, Valgrind, or runtime bounds checkers can spot buffer overflows faster than you can say “unexpected segmentation fault.” Compiler flags like -fstack-protector or security-minded functions like strncpy can also help rein in wild writes. And while not a magic bullet, higher-level languages like Rust or Python have built-in safety nets that make it much harder to fall into these traps in the first place. It’s the difference between racing on a highway without guardrails and cruising on one with plenty of bumpers.
Ultimately, the best prevention strategy is adopting a mindset of respect for memory. Every byte counts, and every boundary matters. Treat your buffers as sacred spaces, not open canvases. Write code that checks, validates, and double-checks before it leaps. Out-of-bounds writes might make for an amusing technical tale, but in practice, they’re as troublesome as a squirrel in an electrical box. So next time your debugger points to an invalid memory access, remember: that’s not just a bug, it’s your code’s way of yelling, “Hey! I’m lost in someone else’s memory!”
When memory goes rogue, it’s both a cosmic joke and a cautionary tale. Out-of-bounds writes teach us that precision isn’t optional—it’s survival. In a world where every byte has a job and every pointer has a destination, a little discipline keeps the comedy from turning into tragedy. So keep your arrays honest, your indexes humble, and your buffers within bounds. After all, the only slapstick you want in your code is the kind that makes you laugh—not the kind that makes your system crash.